What became known as the MINARET program had its basis in earlier efforts to create watch lists initially for suspected threats to the president, for drug dealers, and then, according to the NSA history, for “domestic terrorism.”
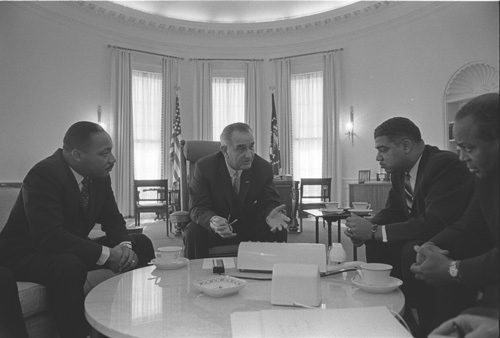 From left to right: Martin Luther King Jr., President Lyndon B. Johnson, Whitney Young, and James Farmer. Lyndon B. Johnson Presidential Library, On-line Photo Archive, W425-21.
From left to right: Martin Luther King Jr., President Lyndon B. Johnson, Whitney Young, and James Farmer. Lyndon B. Johnson Presidential Library, On-line Photo Archive, W425-21.
As civil unrest grew in the late 1960s, President Lyndon Johnson became increasingly concerned that civil rights movements, peace groups, military deserters, and black power organizations were funded by insurgent foreign powers (“Moscow gold”). The federal government was already attempting to automate the monitoring of foreign communications and had slowly taken steps to turn this ear on its own citizens. The effort culminated in 1969 with an program called MINARET.“The project, which became known officially as Minaret in 1969, employed unusual procedures. NSA distributed reports without the usual serialization. They were designed to look like HUMINT reports rather than SIGINT and readers could find no originating agency. Years later the NSA lawyer who first looked at the procedural aspects stated that the people involved seemed to understand that the operation was disreputable if not outright illegal.” 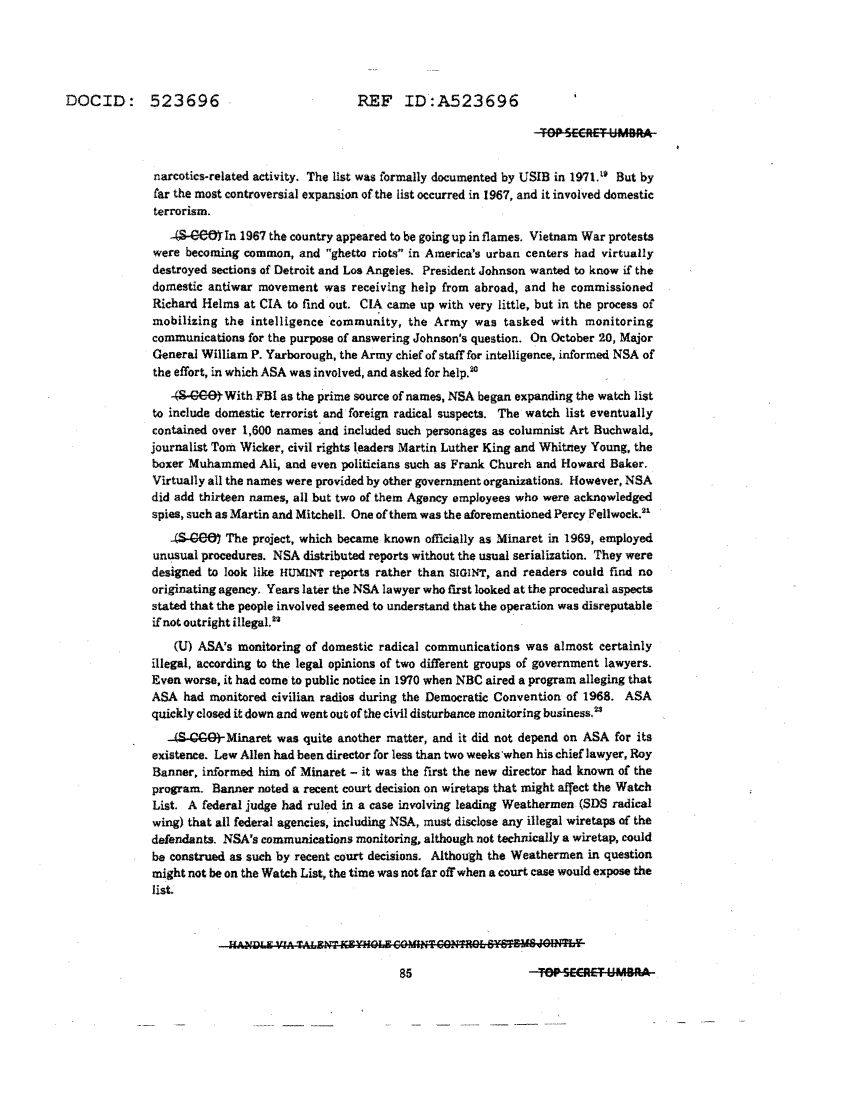 Interagency Security Classification Appeals Panel (ISCAP) July 2013 declassification review by the National Security Archives.
Interagency Security Classification Appeals Panel (ISCAP) July 2013 declassification review by the National Security Archives.
As reported by the New York Times:David Kahn, “Big Ear Or Big Brother?”, The New York Times, May 16, 1976. 
In addition to sucking up and disgorging its daily load of intercepts from abroad, the N.S.A. had improperly eavesdropped on the conversations of many Americans, such as the antiwar protesters Benjamin Spock and Jane Fonda and the Rev. Ralph Abernathy, successor to Dr. Martin Luther King Jr., current director of the National Bureau of Narcotics and Dangerous Drugs and other Government agencies, its vast technological capabilities had invaded the domestic field.
The program included a specific watch list that targeted both Martin Luther King Jr. and Whitney Young (pictured above with President Johnson). It ran totally without judicial oversight or legislative charter. The NSA, which was created to assure the security of American communications and gather intelligence on foreign adversaries, had no authority to target Americans. Regardless, no one at the agency was ever held accountable for breaking the law.
Stretch, Harvest, Tractor, and Rye
The NSA was tasked with broadly monitoring American communications because they had the best tools for the job. The IBM Stretch supercomputer with its custom NSA modules, Harvest, Tractor, and Rye, was the most capable machine of its era. It was specifically built to satisfy the NSA’s “emphasis on manipulation of large volumes of data and on great flexibility and variety in nonnumerical logic processes.”Samuel S. Snyder, “Influence Of U.S. Cryptologic Organizations On The Digital Computer Industry”, Cryptologic Spectrum 7/8, 4/2 (1977/1978).
In other words, the NSA wasn’t looking to process numerical bank statements or compute the routes of subatomic particles, it was processing large amounts of communication data in a variety of formats.
Harvest was a stream processing unit that could process 3,000,000 characters a second. A keyword search could scan roughly 30,000 intercepted messages/minute. There was simply no equivalent machine in the 1960s. Tractor was an enormous magnetic tape unit that could hold 44 billion characters (~40 GB),“Each TRACTOR reel contained an 1800-foot-long tape, capable of holding 120 million characters.”  “The tape reel, together with a take-up reel, was enclosed in a dust-proof cartridge designed to be mounted, dismounted, stored and retrieved by the automated tape library. […] TRACTOR could swap one cartridge for another in 18 seconds.”
“The tape reel, together with a take-up reel, was enclosed in a dust-proof cartridge designed to be mounted, dismounted, stored and retrieved by the automated tape library. […] TRACTOR could swap one cartridge for another in 18 seconds.” 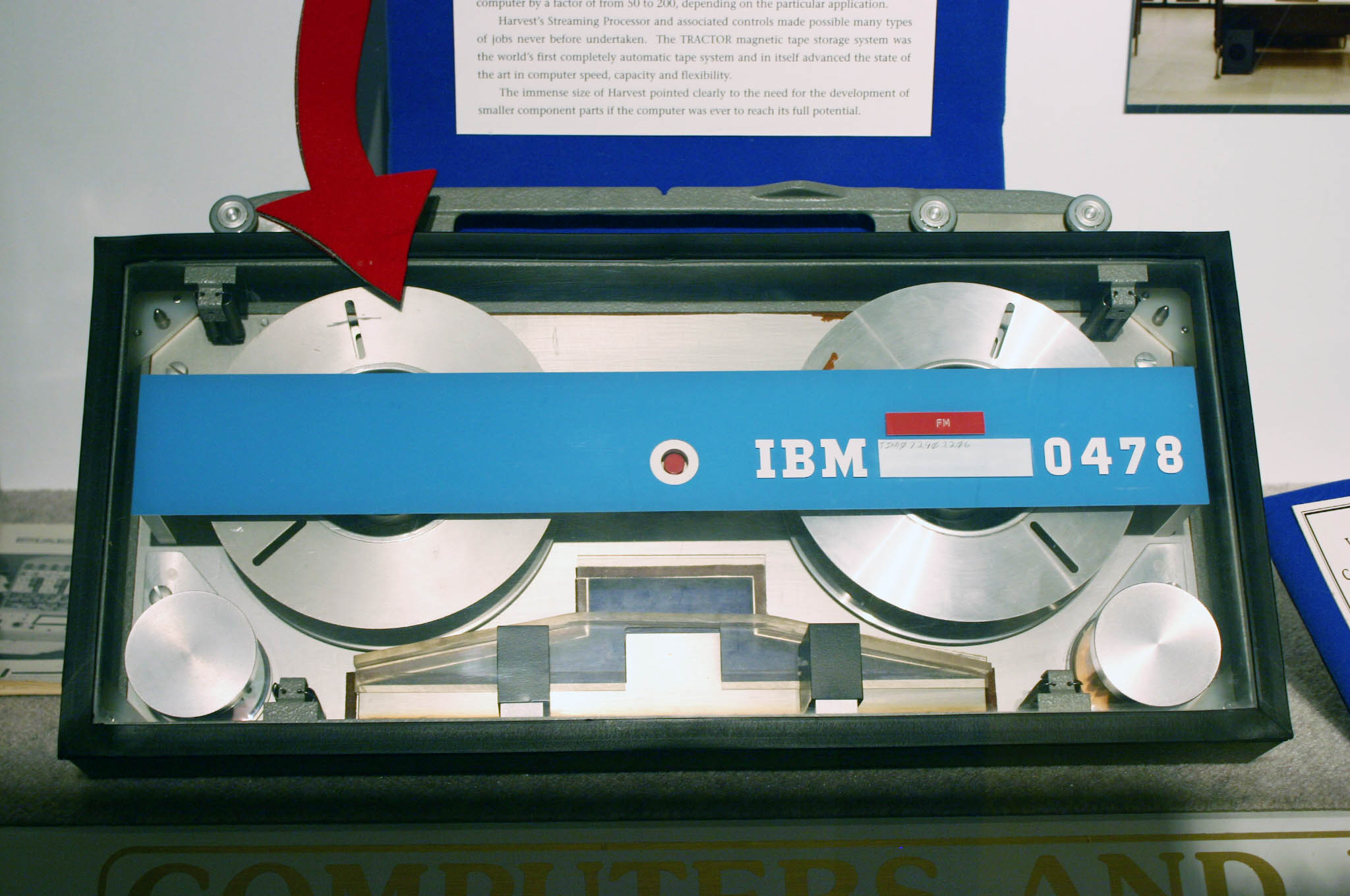 “IBM Archives: TRACTOR”, ibm.com, 2003
“IBM Archives: TRACTOR”, ibm.com, 2003
and Rye offered remote terminal access that allowed agents abroad to input signals intelligence.
Before the assassination of King ignited days of civil unrest, signals intelligence used computers to help in the government effort to defame King and undermine his cause. Large organizations have always invested in machines like Stretch because information is often the most effective weapon in a conflict.
As America is once again gripped in strife, remember that there was a time when widely admired citizens like Martin Luther King and Whitney Young were suspected of being domestic terrorists by their own government. The narrative can change. But we must overcome the disinformation and fear that has overtaken the United States.